I've been trying to make openvpn client work on ubuntu 20.04 but could not. This is the config I'm using on a mac, windows and my ubuntu machine: client dev tap0 proto tcp dev-node MY-VPN //only on windows remote my.server.ip 12974 resolv-retry infinite nobind persist-key persist-tun ca ca.crt cert cert.crt key key.key cipher AES-128-CBC comp.
- I've been trying to make openvpn client work on ubuntu 20.04 but could not. This is the config I'm using on a mac, windows and my ubuntu machine: client dev tap0 proto tcp dev-node MY-VPN //only on windows remote my.server.ip 12974 resolv-retry infinite nobind persist-key persist-tun ca ca.crt cert cert.crt key key.key cipher AES-128-CBC comp.
- OpenVPN provides flexible VPN solutions to secure your data communications, whether.
Highlighted Articles Discussion Group | On This Page Stop if you have a 'Deployed' version of Tunnelblick. It comes already set up — you do no need to do anything more. Fashion designer sketch drawing. Just start using it and enjoy! Stop if you have purchased VPN service from a VPN service provider. They should provide you with configuration files and instructions on how to use them with Tunnelblick. Stop if you have VPN service from a corporate or other network provided by your employer. Your network manager or IT department should provide you with configuration files and instructions on how to use them with Tunnelblick. Stop if want details about the structure of a Tunnelblick VPN Configuration, see '.tblk' Details. Otherwise, continue! Setting Up and Installing ConfigurationsFirst, install Tunnelblick and launch it so it is running. It is not enough to install Tunnelblick: you also need to tell Tunnelblick how to connect to a VPN. You tell Tunnelblick how to connect to a VPN with a configuration file. If you already have configuration files you can install them by dragging and dropping them onto the Tunnelblick icon in the menu bar. After installing your configurations, continue with 'Set Nameserver' Check Box and DNS & WINS Settings, below. If you don't have configuration files or you want more information about them continue reading. Tunnelblick can use two types of configuration files:
Converting OpenVPN Configurations to Tunnelblick VPN ConfigurationsYou can drag and drop OpenVPN configurations onto the Tunnelblick icon in the menu bar and they will be installed as Tunnelblick VPN Configurations. Creating and Installing a Tunnelblick VPN ConfigurationTo create a Tunnelblick VPN Configuration:
When you install, you will be asked if you want each configuration to be private or shared. A private configuration may only be used when you are logged onto the computer. A shared configuration may be used by anyone who is logged into the computer. If the name you have given conflicts with the name of an existing installed configuration, you will be given the opportunity to change the name. The process of installation will copy the .tblk to a special location on your computer (see File Locations) and make changes to it so it can be used securely. You can then delete the original .tblk you created, or move it somewhere convenient as a backup, or copy or move it to another computer and install it on that computer. That's it! You are done. The configuration(s) will be available immediately in Tunnelblick. Modifying a Tunnelblick VPN ConfigurationYou can modify a Tunnelblick VPN Configuration two ways:
Files Contained in a Tunnelblick VPN ConfigurationThe files that should be contained in a Tunnelblick VPN Configuration (the 'files related to the connection' above) should all be 'plain text' files:
The 'Set Nameserver' Check Box and DNS & WINS SettingsIf you are using DHCP, wish to use DNS and WINS servers at the far end of the tunnel when connected, and the VPN server you are connecting to 'pushes' DNS and WINS settings to your client, select 'Set nameserver'. (This is the situation for most users.) If you are using DHCP, wish to use your original DNS and WINS servers when connected, and the VPN server you are connecting to does not 'push' DNS or WINS settings to your client, select 'Do not set nameserver'. If you are using manual settings, different versions of macOS behave differently. This is due to a change in network behavior in Snow Leopard and is beyond the scope of this project to fix. If you're using Leopard (OS X 10.5) or Tiger (OS X 10.4), then it is possible to use the VPN-server-supplied DNS and WINS settings in addition to your manual settings by selecting 'Set nameserver'. However, your manual settings will always take precedence over any VPN server-supplied settings. If 'Do not set nameserver' is selected, you will continue to use only your manually-configured settings and any VPN server-supplied settings will be ignored. 'Take precedence' means that the manual DNS server will be used for all DNS queries unless it fails to answer, in which case the VPN server-supplied DNS server will be used. If you are using Snow Leopard (OS X 10.6) or later, then your usual DNS and WINS settings will always be used, and no aggregation of configurations will be performed.
If your situation is not described above (e.g., if you use manual DNS settings and wish to use DNS servers at the far end of a tunnel when connected, or you wish to use the macOS ability to use different nameservers for different domains), you must create your own up/down scripts and select 'Set nameserver'. The OpenVPN --user and --group options and openvpn-down-root.soWhen using 'Set nameserver' or your own down script for OpenVPN, it is usually necessary to avoid using the OpenVPN 'user' and 'group' options in the configuration file. These options cause OpenVPN to drop root privileges and take the privileges of the specified user and group (usually, 'nobody'). If this is done, then the down script that handles restarting connections when there is a transient problem fails, because it is run without root privileges. OpenVPN usually fails, too, if your configuration performs any routing (most configurations do). However, Tunnelblick includes the 'openvpn-down-root.so' plugin for OpenVPN. When this plugin is activated, OpenVPN still drops root privileges and runs as the specified user:group after a connection is made, but runs the down script run as root:wheel, so reconnecting after transient network problems can work if OpenVPN does not need to restore any routes. When you connect with a configuration that includes the 'user' and/or 'group' options in the configuration file, Tunnelblick will ask if you wish to use the openvpn-down-root plugin. Answer 'yes' and Tunnelblick will use the plugin each time it makes a connection. OpenVPN will still be unable to make route changes after the initial connection; they have to be made in the your own customized scripts. |
I wanted to use Steam’s in-home streaming feature outside of my home. It turns out that you can do this via VPN. OpenVPN is relatively simple to setup in TUN mode, but TAP mode is more complicated due to bridging.
It took gathering information from a few different sources (referenced at the end of this article) to produce an up-to-date tutorial for a TAP-based VPN configuration.
Topology
This is our basic network topology, or rather, the topology we hope to configure towards:
Router & DHCP Server
IP: 192.168.1.1
DHCP Range: 192.168.1.10 to 192.168.1.237
VPN Server
IP: 192.168.1.206 (DHCP Reservation)
VPN Clients IP Range: 192.168.1.238 - 192.168.1.254
Server Setup
Install OpenVPN, bridge tools, and Easy-RSA
Configure Bridged Interface
Although you will see examples of bridge configurations with static addresses defined, this did not work for me. I would not be able to access the outside internet. I looked into the ubuntu wiki on bridging (see references) and discovered a configuration for a simple, dhcp based bridge. This worked best for me. Everything after bridge_ports is from a different TAP tutorial – I don’t know what they do!
The simplest way to check this is to reboot shutdown -r now and then test if the outside internet is still accessible ping google.com and to look at the output of ifconfig. Vernissage in english.
Configure OpenVPN

Extract the example VPN server configuration into /etc/openvpn.
Open the server config, e.g. vim /etc/openvpn/server.conf
Configure the following, yours may be different depending on your topology:
Create the scripts that will execute when the OpenVPN service starts and stops. These scripts add and remove the OpenVPN interface to the servers br0 interface.
/etc/openvpn/down.sh
/etc/openvpn/up.sh
Make these scripts executable
Generate the keys
Copy over the easy-rsa variables file and make the keys directory
Open up /etc/openvpn/easy-rsa/vars and configure your defaults, e.g.
You must also set the KEY_NAME='server', the value is referenced by the openvpn config.
Generate the Diffie-Hellman parameters
Now move to the easy-rsa dir, source the variables, clean the working directory and build everything:
Make sure that you responded positively to the prompts, otherwise the defaults are no and the key creation will not complete.
Next, move the key files over to the openvpn directory
You’re ready to start the server
Tunnelblick Ubuntu 20.04

If the server is not running, look in /var/log/syslog for errors
Generate Certificates and Keys for Clients
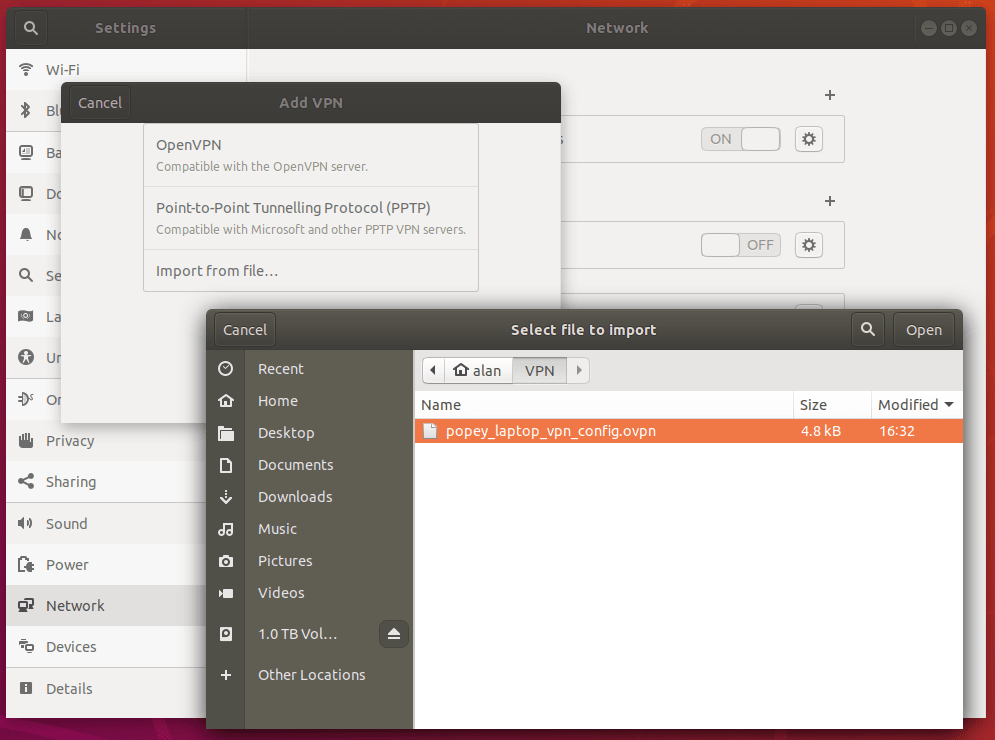
So far we’ve installed and configured the OpenVPN server, created a Certificate Authority, and created the server’s own certificate and key. In this step, we use the server’s CA to generate certificates and keys for each client device which will be connecting to the VPN. These files will later be installed onto the client devices such as a laptop or smartphone.

To create separate authentication credentials for each device you intend to connect to the VPN, you should complete this step for each device, but change the name client1 below to something different such as client2 or iphone2. With separate credentials per device, they can later be deactivated at the server individually, if need be. The remaining examples in this tutorial will use client1 as our example client device’s name.
As we did with the server’s key, now we build one for our client1 example. You should still be working out of /etc/openvpn/easy-rsa.
Again you need to respond positively when presented with yes or no prompts. You should not enter a challenge password.
Tunnelblick Ubuntu Emulator
You can repeat this section again for each client, replacing client1 with the appropriate client name throughout.
The example client configuration file should be copied to the Easy-RSA key directory too. We’ll use it as a template which will be downloaded to client devices for editing. In the copy process, we are changing the name of the example file from client.conf to client.ovpn because the .ovpn file extension is what the clients will expect to use.
Edit the client profile to reflect your server’s IP address and configure it for tap. Also be sure to replace my-server-1 with your VPN server’s IP or domain name.
Soldat 2 for mac. /etc/openvpn/easy-rsa/keys/client.ovpn
Finally, you can transfer client1.crt, client1.key, client.ovpn, and ca.crt over to your client.
Create and download Tunnelblick Config (Mac only)
Now you can scp that over to your Mac, double-click to extract, and then double-click the .tblk file to allow Tunnelblick to install the profile.
It connects, I can ping the OpenVPN server’s LAN address, but no internet or other LAN addresses.
Are you running on VMWare VSphere or ESXi? If so you need to configure your switch in promiscuous mode.
It connects, I can ping LAN and internet addresses, but DNS isn’t working.
If you manually configure a DNS (e.g. 8.8.8.8), does it work? Then you can configure your openvpn server to push DNS configuration to the clients.
Add a line like this to the openvpn server config:
References
